We love Raspberry Pis! If you don’t have one then you should get one. They are a great introduction to Linux and work well with our service. We recommend a Raspberry Pi 5 with 4GB or 8GB of memory. Parts of the Nettica Agent were written on a Pi, and we have Pi-specific builds in our Debian and Docker repos. With a Raspberry Pi on your home network, you can use Nettica VPN service and WireGuard to enable subnet routing, which then allows you to access your entire home network from anywhere, for free. Plus, the device itself has many capabilities. You can run a web server, media player, or even a video conferencing server. It’s a powerful little box.

Overview
Our service allows you to quickly and correctly configure WireGuard in a scalable manner. If you’ve ever set up WireGuard by hand, then you already know how difficult it is to maintain and synchronize configurations. That’s where we come in. We provide a control panel that lets you fully configure WireGuard to meet your needs, and then will automatically update your hosts in near real-time as changes are made.
We employ a zero-trust model for our service. What does that mean? In short, all access is validated and there is no trust between devices by default. We allow you to use your Google or Microsoft accounts to sign in to our service. While we do offer an option of signing up with us directly, we’d rather you maintain one less password and use your existing authentication provider, with all of its multi-factor authentication (if enabled). Enterprise customers will be happy to know we can integrate with your Google or Microsoft Entra ID and then automatically give your employees access.
Installation on Raspberry Pi
First, let’s install the Nettica Agent on your Raspberry Pi. We support both the 32-bit and 64-bit Raspberry Pi OS variants. Open a terminal and enter the following:
sudo apt install curl -y # just in case
sudo curl -s -o /etc/apt/sources.list.d/nettica.list https://ppa.nettica.com/nettica.list
curl https://ppa.nettica.com/nettica.gpg | sudo gpg -o /usr/share/keyrings/nettica.gpg --dearmor --batch --yes
sudo apt update
# Install wireguard if not already installed, as well as resolvconf
sudo apt install wireguard resolvconf rdesktop iptables
# Install nettica-client and then nettica.agent
sudo apt install nettica-client nettica.agent
# Install Remote Desktop for Pi (optional, but very useful)
sudo apt install xrdp
# Enable packet forwarding for IPv4 and IPv6
sudo sed -i "s/#net.ipv4.ip_forward=1/net.ipv4.ip_forward=1/g" /etc/sysctl.conf
sudo sed -i "s/#net.ipv6.conf.all.forwarding=1/net.ipv6.conf.all.forwarding=1/g" /etc/sysctl.conf
# Reload the config
sudo sysctl -p
nettica.agent &Copy and paste the code block above into the terminal window to install the Nettica Agent. It will automatically install the version appropriate for your Pi.
Create a Network
The next thing to do is make a network on Nettica. To make a network, use a browser to log in to the Nettica Admin, click on Networks, and then click the blue banner which automatically creates your first network.
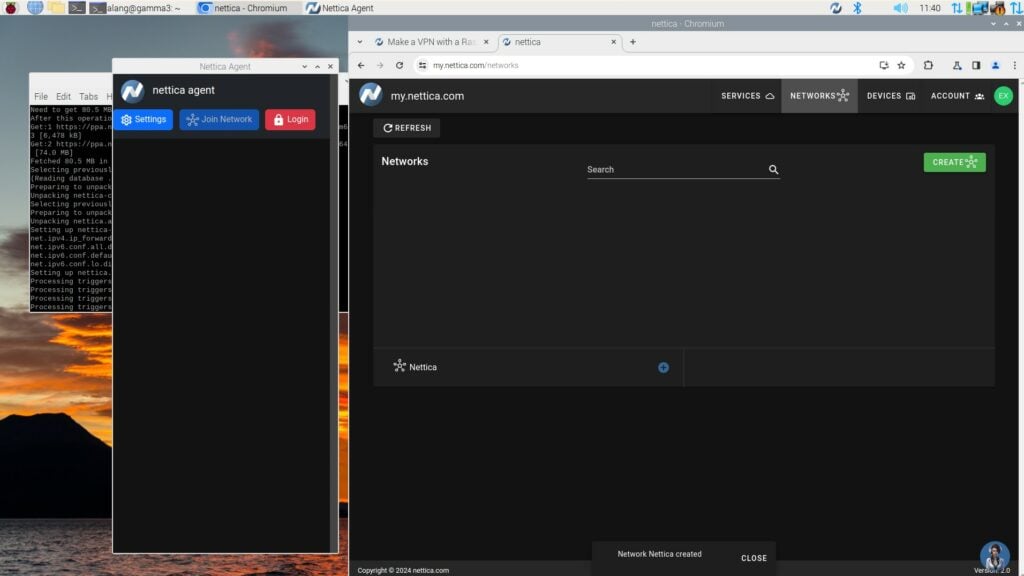
You’ll find the Nettica Agent under Internet in the start menu. Open it and log in using the same credentials you used previously. If you used the code block above, it automatically started.
Click “Join Network” and complete the form. Click Submit and a few seconds later, your pi will be configured.
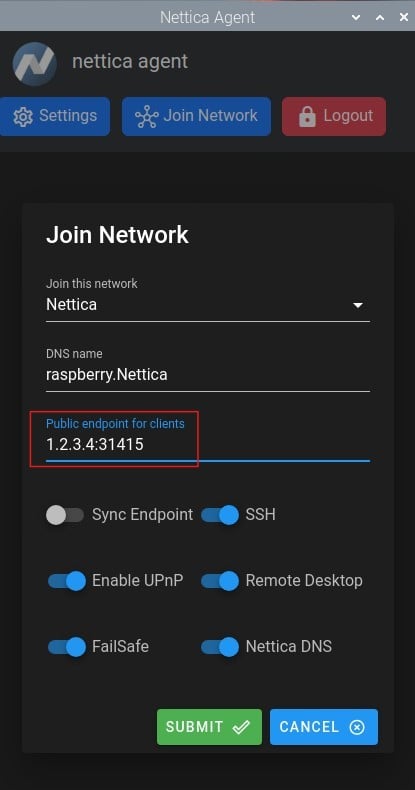
For the public endpoint, enter it as shown above. We like using 31415 for the port number. Enabling UPnP will automatically update your public endpoint to your real external IP address. If the address fails to update, also enable Sync Endpoint, which will update the IP address from our servers. Note that if UPnP is unavailable, you must manually configure port forwarding.
Enable Subnet Routing on a Raspberry Pi
Note: As of bookworm, Raspberry Pi OS no longer installs iptables by default. You may have noticed we installed it above. This is needed to configure subnet routing.
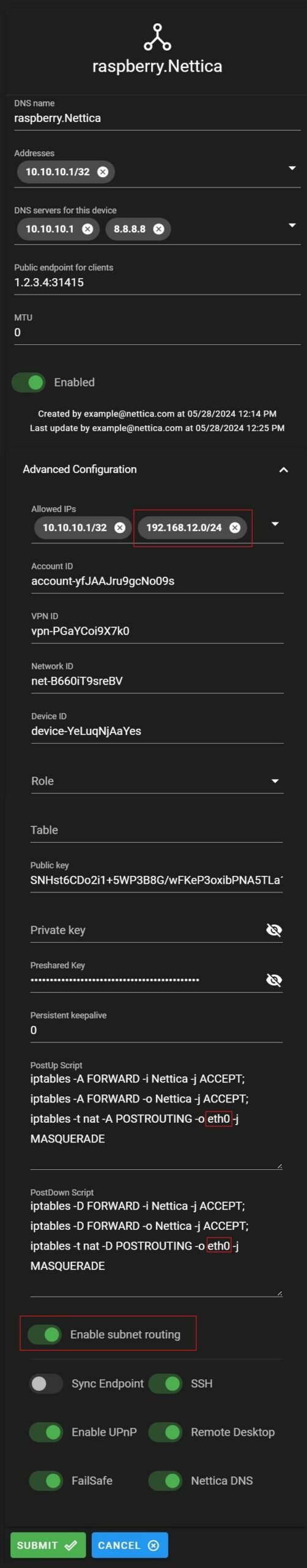
Enabling subnet routing allows you to connect to other machines besides the Raspberry Pi. To do this, log in to the Admin Console again, click “Networks”, expand the Nettica network, and then select your pi. Then click edit in the right-hand pane. Click “Advanced Configuration”.
Enable subnet routing and add your home’s local subnet, 192.168.12.0/24 in the example below, to the Allowed IPs. Click Submit, and then go back and edit the entry again. You’ll notice that PostUp and PostDown scripts have been written for you. These are the proper values for a Raspberry Pi using the wired connection, eth0.
But Raspberry Pi 4s and above come with two network connections. We recommend the wired connection connected directly to your internet gateway. However, if that’s not possible, it also has built-in Wi-Fi. If you’re using Wi-Fi, modify the PostUp and PostDown scripts to point to wlan0 instead of eth0.
Click Submit. After a moment you’ll get a notification on your Pi that the network has been updated. You are now completely set up to remotely connect to your Raspberry Pi and your entire home network.
Test your Connection to the Raspberry Pi
Install the Nettica Agent on your laptop. Note that you do not need to specify a public endpoint as it is acting as a client. Tether your laptop to your phone’s Internet. You should now be able to connect back to your Pi directly, as well as all the other machines in your home. The packets for your home network are routed through the Pi after being securely transported using WireGuard. And then the reverse happens with the responses, with the Pi securely encrypting the traffic back to your laptop.
To test it, open a command prompt and type ping 10.10.10.1 and then hit enter. You should see responses coming from your Pi. Now type ping 192.168.12.1, but using your subnet. That should work as well. You now have full access to your home network.
Enabling Nettica DNS does not cause name resolution for machines in your home network that do not have a Nettica Agent. However, you can still connect to them by IP address, or you can add your home resolver (usually the IP address of your gateway) to the DNS servers list. It’s very flexible, feel free to test this yourself. If you have any problems reach out to Nettica Support; they are experts at this.
Conclusion
Today we learned how to configure a Raspberry Pi with WireGuard and the Nettica VPN Service, to connect to our entire home network. We did this by enabling subnet routing through PostUp and PostDown scripts. This knowledge translates: You can do the same thing with a Linux-based host in the cloud. You might have to use a different interface name for your network connection, but everything else remains the same.
Bonus Points
If you successfully completed this tutorial, then congratulations! However, you might have one last lingering question. Can I make my laptop, connected to my phone, route all traffic back through my home’s network? That way it looks like I’m home, even when I’m somewhere else. Yes, you can! To do this enter 0.0.0.0/0 into the Allowed IPs for your Raspberry Pi. This will cause all packets from your laptop to be routed through your home network. Give it a minute to update, and viola, you’re connected.
You can remove the 0.0.0.0/0 to turn it off. You might find your connection slow unless you have symmetric high-speed Internet at home. Most Internet connections are asymmetric, with slower upload speeds than download. In this configuration, you’re using your home’s upload bandwidth and likely maxing it out.
Special Note to Raspberry Fanatics: Our completely open-source Nettica Admin will run on a Raspberry Pi 5. That’s not relevant to this article, but just sayin’. Don’t forget to install MongoDB!
More Info
Check out our Getting Started Guide to learn more about making your own VPN, with or without a Pi.
If your home network is behind a carrier-grade NAT, this configuration will fail. However, we have a solution. Check out our relay services, which solve the problem regardless of your ISP.
Related Reading
Use Docker & WSL2 to access your home network with WireGuard
WireGuard NAT Traversal Made Easy